OpenVPN Client/Server Implemenation
==== key signing ====
You can host the certificate authority on the vyos device itself. This is obviously not as secure as hosting it on a separate system. If someone was to get into the vyos they would have access to all your keys and would be able to sign new keys against the CA. Nonetheless, it is convenient and secure-enough for many sites. This is how it can be done.
From the VyOS, copy the easy-rsa directory into /config, where it won’t get lost on an upgrade.
cp -rv /usr/share/doc/openvpn/examples/easy-rsa/2.0/ /config/easy-rsa2
vi /config/easy-rsa2/vars
edit the options at the bottom of /config/easy-rsa2/vars to personalize them. Increasing KEY_SIZE to 2048 is recommended. Also, you can increase the certificate authority and key expiration. These are the defaults:
...
# Increase this to 2048 if you
# are paranoid. This will slow
# down TLS negotiation performance
# as well as the one-time DH parms
# generation process.
export KEY_SIZE=1024
# In how many days should the root CA key expire?
export CA_EXPIRE=3650
# In how many days should certificates expire?
export KEY_EXPIRE=3650
export KEY_COUNTRY="US"
export KEY_PROVINCE="CA"
export KEY_CITY="SanFrancisco"
export KEY_ORG="Fort-Funston"
export KEY_EMAIL="me@myhost.mydomain"
now load the variables
$ cd /config/easy-rsa2/
$ source ./vars
start fresh in case there is something old lingering around in there. This will delete all keys, etc.
$ ./clean-all
Build the certificate authority files
$ ./build-ca
Build the diffie-hellman key exchange
$ ./build-dh
Build the key for the server
$ ./build-key-server js-server
Copy the certs and keys into /config/auth
sudo cp /config/easy-rsa2/keys/ca.crt /config/auth/
sudo cp /config/easy-rsa2/keys/dh1024.pem /config/auth/
sudo cp /config/easy-rsa2/keys/js-server.key /config/auth/
sudo cp /config/easy-rsa2/keys/js-server.crt /config/auth/
Now you can build the key for the client and distribute to them
use ./build-key to generate a certificate that will connect to the vpn without a pass-phrase and ./build-key-pass if you want the user to enter a pass-phrase before connecting. ./build-key-pass is more secure in case someone steals your certificate and key they will still need to enter a password to connect.
$ ./build-key jimmy
answer all questions accordingly and be sure to answer yes to “Sign the certificate?” the “1 out of 1 certificate requests certified, commit?”
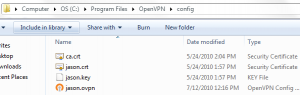
Now copy the keys and certs and create a config for Jimmy to remote in with. This is how I do it.
first make a directory for the client in /config/easy-rsa2/keys
cd /config/easy-rsa2/keys
mkdir jimmy
cp jimmy* jimmy/
cp ca.crt jimmy/
create a client config with your favorite text editor,
vi jimmy/jsvpnserver.ovpn
and add the following
client
proto udp
remote-cert-tls server
verb 2
dev tun0
cert jimmy.crt
key jimmy.key
ca ca.crt
remote [vpn-server host or ip] 1194
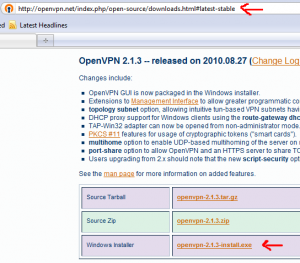
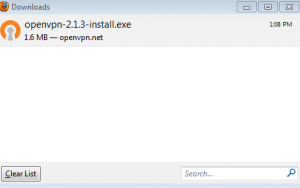
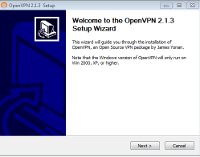
From your local computer download the config directory (jimmy) from the vpn server
$ scp -r vyos@10.101.101.1:/config/easy-rsa2/keys/jimmy .
this copies the jimmy directory into the current directory on your computer (the period designates current directory). If your on MS Windows you will need to use cygwin or putty-scp to do this. Also, if using MS Windows you will need to run unix2dos on those files
from your computer where you downloaded the jimmy folder to.
unix2dos jimmy/*
I wrote a script to do all this for you -> http://jasonschaefer.com/stuff/easyrsa-user-setup-vyos.sh.txt
Setting up the OpenVPN Server
The server subnet needs to be a different subnet from your LAN. Set it to something unique that will be unlikely on any remote networks your clients will be on.
The “–push route 10.101.101.0 255.255.255.0” needs to be changed to the subnet on the LAN of the router. The one you will VPN in to access.
set interfaces openvpn vtun0 mode server
set interfaces openvpn vtun0 server subnet 10.206.109.0/24
set interfaces openvpn vtun0 server name-server 10.101.101.1
set interfaces openvpn vtun0 server domain-name jasonschaefer.com
set interfaces openvpn vtun0 server push-route 10.101.101.0/24
set service dns forwarding listen-on vtun0
set interfaces openvpn vtun0 tls cert-file /config/auth/js-server.crt
set interfaces openvpn vtun0 tls key-file /config/auth/js-server.key
set interfaces openvpn vtun0 tls ca-cert-file /config/auth/ca.crt
set interfaces openvpn vtun0 tls dh-file /config/auth/dh1024.pem
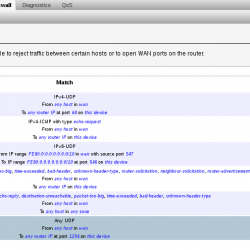
#Set the firewall to allow openvpn through
set firewall name wan-local rule 40 action accept
set firewall name wan-local rule 40 destination port openvpn
set firewall name wan-local rule 40 protocol udp
commit
save
Thats it! Your done!
STATIC CLIENT ADDRESS
The static ip address for each client is done with this command:
set interfaces openvpn vtun0 server client leroy ip 10.206.109.123
The name “leroy” is the Common Name of the certificate. After this is committed leroy will receive .123 on his laptop each time he connects to the vpn.
ROUTING VARIOUS LAN’s OVER VPN
The routing between a remote LAN (iroute) is done like this:
set interfaces openvpn vtun0 server client leroyhome ip 10.206.109.0.3
set interfaces openvpn vtun0 server client leroyhome subnet 10.101.103.0/24
The “subnet” option is openvpn’s internal route (iroute) function. This tells openvpn what the remote LAN subnet is. In this example, 10.101.103.0/24 is leroys house LAN.
Now you can add a static route in order to route to this remote LAN.
set protocols static route 10.101.103.0/24 next-hop 10.206.109.1
10.206.109.1 is the openvpn routers interface vtun0 ip address.
If your designing a network with multiple remote sites its convenient to make their addresses contiguous and route to them all with a single route.
10.101.101.0/24 (my house)
10.101.102.0/24 (geoff’s house)
10.101.103.0/24 (leroy’s house)
I use subnetcalc to figure out the host ranges
$ subnetcalc 10.101.101.0/22
Host Range = { 10.101.100.1 - 10.101.103.254 }
- 10.101.101.0 is a HOST address in 10.101.100.0/22
So, a slash 22 cover from .100-.103, that’s perfect for our small network.
set protocols static route 10.101.100.0/22 next-hop 10.206.109.1
and you need to push this route to all the clients
set interfaces openvpn vtun0 server push-route 10.101.100.0/22
SITE TO SITE VPN
basic instructions:
generate the passive key for head office from inside the easyrsa folder
source ./vars
./build-key-server site2site_server-passive
scp keys/site2site_server-passive.* user@vpn-server-passive-host:/config/auth/
#active key for branch office, this side initiates the vpn handshakes
./build-key site2site_active
scp keys/site2site_active.* user@vpn-server-active-host:/config/auth/
active site files in /config/auth/
ca.crt,
site2site_active.key,
site2site_active.crt
passive site files in /config/auth/
ca.crt,
site2site_server-passive.key,
site2site_server-passive.crt,
dh1024.pem
==================
#site to site openvpn
set interfaces openvpn vtun9
set interfaces openvpn vtun9 local-address 172.16.9.[1 | 2]
set interfaces openvpn vtun9 remote-address 172.16.9.[1 | 2]
set interfaces openvpn vtun9 remote-host [remote-vpn-host]
#standard openvpn port is 1194, best used for client/server mode. prevents ovpn config from needing port setting
set interfaces openvpn vtun9 local-port 1195
set interfaces openvpn vtun9 remote-port 1195
set interfaces openvpn vtun9 mode site-to-site
set interfaces openvpn vtun9 tls ca-cert-file /root/ca.crt
#the passive site cert/key needs to be signed as a server!
set interfaces openvpn vtun9 tls key-file /root/[passive.key | active.key ]
set interfaces openvpn vtun9 tls cert-file /root/[passive.crt | active.crt]
set interfaces openvpn vtun9 tls role [active | passive]
#dh1024.pem is required on passive host only!
set interfaces openvpn vtun9 tls dh-file /root/dh1024.pem
commit;save
#open firewall for openvpn
set firewall name wan-local rule 20 action accept
set firewall name wan-local rule 20 destination port 1195
set firewall name wan-local rule 20 protocol tcp_udp
#set static routes to networks on other side of vpn, if any
set protocols static route 192.168.7.0/24 next-hop 172.16.9.[1 | 2]
set protocols static route 192.168.8.0/24 next-hop 172.16.9.[1 | 2]
commit;save
DYNAMIC DNS
How to reach your vpn server and avoid using a static ip. We will be using afraid.org to automatically update a hostname’s A record with the public ip of your Vyos VPN server.
You will need to register for an account at https://freedns.afraid.org. Then create a subdomain, for this example it will be myvpnserver.mooo.com. Go to the “Dynamic DNS” section and copy the “Direct URL”.
Create a script under /config/scripts on your Vyos.
vi /config/scripts/myvpnserver.mooo.com.sh
#!/bin/bash
/usr/bin/curl -k [paste your direct url here]
Make it executable
chmod 755 /config/scripts/myvpnserver.mooo.com.sh
Now tell Vyos to run this with cron.
set system task-scheduler task dynamicDNS executable path /config/scripts/myvpnserver.mooo.com.sh
set system task-scheduler task dynamicDNS interval 15m
REVOKE KEYS ON VYOS
vyos@router:~$ cd /config/easy-rsa2/
vyos@router:/config/easy-rsa2$ ./revoke-full jimmy
Using configuration from /config/easy-rsa2/openssl.cnf
Revoking Certificate 0E.
Data Base Updated
Using configuration from /config/easy-rsa2/openssl.cnf
jimmy.crt: /C=US/ST=NM/L=SantaFe/O=Blah/CN=jimmy/emailAddress=jimmy@localhost.local
error 23 at 0 depth lookup:certificate revoked
The error 23 at 0 … is normal and expected.
Now copy the updated CRL (certificate revocation list) to /config/auth
vyos@router:/config/easy-rsa2$ cp keys/crl.pem /config/auth/
If this is the first revocation you need to add it to the config as well:
vyos@router:~$ configure
vyos@router# set interfaces openvpn vtun0 tls crl-file /config/auth/crl.pem
vyos@router# save; commit; exit
Saving configuration to ‘/config/config.boot’…
Done
No configuration changes to commit
exit
VERIFY REVOKED CERTIFICATES
You can verify the revoked keys with the openssl command
vyos@router:~$ openssl crl -in /config/auth/crl.pem -text
…
Revoked Certificates:
Serial Number: 08
Revocation Date: Jan 30 00:19:24 2016 GMT
Serial Number: 0E
Revocation Date: Jul 13 22:51:50 2016 GMT
…
In the above example keys 08 and 0E have been revoked
vyos@router:~$ cat /config/easy-rsa2/keys/index.txt
…
V 230804225528Z 02 unknown /C=US/ST=NM/L=SantaFe/O=SITC/CN=jason/emailAddress=jason@local
R 230806213443Z 160130001924Z 08 unknown /C=US/ST=NM/L=SantaFe/O=Blah/CN=john/emailAddress=john@localhost
R 260711225142Z 160713225150Z 0E unknown /C=US/ST=NM/L=SantaFe/O=Blah/CN=jimmy/emailAddress=jimmy@localhost.local
…
From this file index.txt, you can ascertain which serial numbers belong to which users!